According to SHRM, 59% of U.S. employers allow employees to work from locations outside of the office. And as technology continues to get better, we see that percentage increasing in the future. In order to understand the insurance concerns for telecommuters and employees on business travel, it’s important to identify the types of telecommuters.
4 Types of Telecommuters
1. As Needed Remote Worker. Someone who needs to work from home on an as needed basis or due to a company emergency. For example, an office power outage, inclement weather, illness, sick family member or home maintenance issues.
2. Flexible Arrangement Worker. Someone who works from home part time, on a regular basis. For example, arriving later to work to take kids to school or working from home one or two days a week for family obligations.
3. Remote Worker. Someone who works from home 100% of the time. This could be because the employee moved out of the area and transferring a client relationships is far more difficult than setting up the employee to work from home.
4. Mobile Employee. Someone whose duties requires them to be out of the office on a constant basis. Jobs that are heavy with sales, repair work or on-site auditing would be good examples of a mobile worker.
How to Make a Successful Work from Home Program
- Identify which employees have sufficient institutional knowledge and experience to be considered for a flex arrangement.
- Evaluate the different communication and collaborative tools such as Skype and GoToMeeting.
- Establish guidelines and requirements for the home office (i.e. location, furniture, equipment, etc.).
- Provide training in office ergonomics (our Safety and Loss Control Department at Gunn-Mowery can come to your office to assess the ergonomics of your staff)
Check your Workers Compensation Policy
In the 1910’s, The Department of Labor and Industry established the Workers Compensation Act to provide predictable coverage for medical bills and lost wages for employees injured while on the job. In return for these benefits, the worker gives up the right to sue the employer. In general, the Act provides coverage for medical expenses and wage loss for injuries sustained by employees while in the course and scope of employment. These benefits vary in amounts from State to State.
When reviewing your Insurance policy, you should see Workers Compensation Coverage (make sure it lists the right State!), as well as Employers Liability Insurance. Under the Employers Liability Coverage is where it will list the bodily injury by accident amounts per accident and per employee. If the business owns the property, it should be added to your property coverage. However, an employee working from home typically has $2,500 of coverage on their homeowners policy for business personal property if the property is owned by the employee and not the employer. Make sure you discuss with your agent of the location should be scheduled for liability…and your employee should have the same discussion with their agent.
Remote Work Means a Data Security Policy is CRITICAL
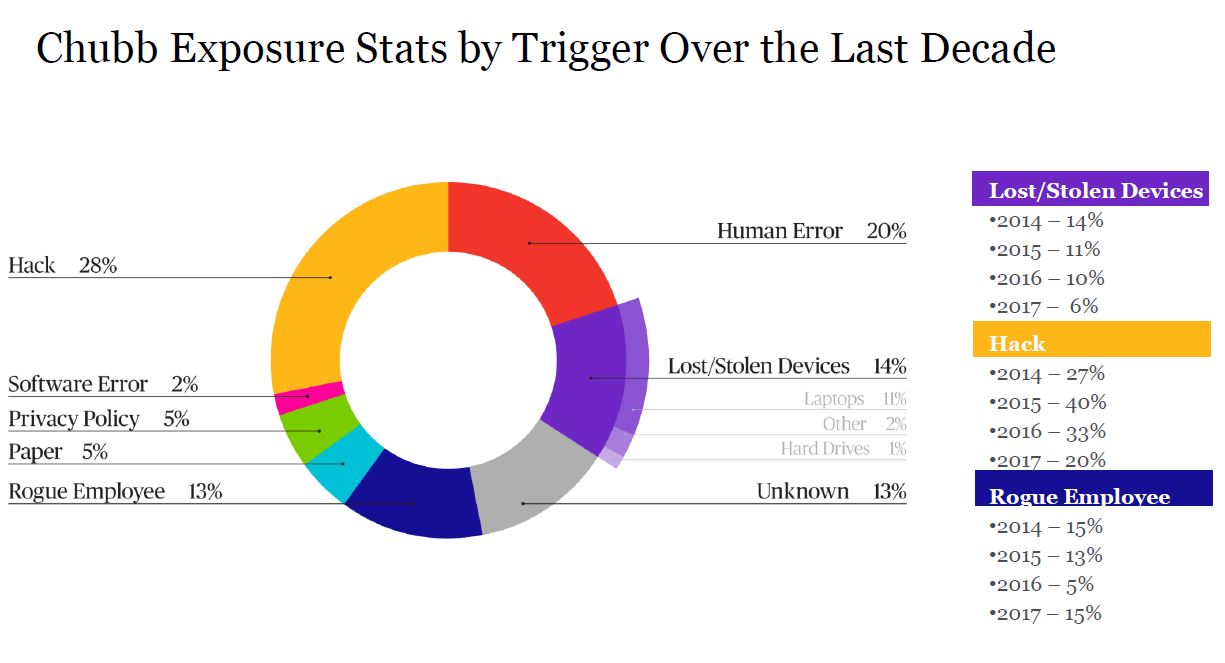
According to Chubb’s claims data as of October 2017, human error made up 20% of claims (i.e. opening spam emails, clicking on suspicious links, opening attachments, etc.) and lost/stolen devices was 14% of claims submitted. Therefore, 34% of claims could have been prevented if companies had better security policies in place.
Here are 9 key elements that we believe make a successful data security policy:
1. Safeguard Data Privacy. Employee and customer data should be kept confidential and secure. Did you know that medical equipment supplier, Lincare, was fined $239,800 as a result of a breach which occurred when an employee left unprotected healthcare information in a car in the possession of her estranged husband? An administrative Law Judge upheld the penalty, noting that Lincare did not have policies in place requiring employees to safeguard medical information off-site.
2. Establish Password Management. Your policy should cover all employees, plus temporary workers. Passwords should never be shared and password complexity standards should be established. (A good complex password would be 8 characters at a minimum, use uppercase letters, lowercase letters, numbers and special characters and be changed every few months.)
3. Govern Internet Usage. Balance your need for employee productivity with restrictions based on your security concerns.
4. Manage Email Usage. Email is a favorite way for hackers to steal information. Set clear standards for message content, encryption and file retention.
5. Govern and Manage Company-Owned Mobile Devices. Implement a formal process. At a minimum, require employees to protect their devices from theft and establish password protection.
6. Establish an Approval Process for Employee-Owned Mobile Devices. Use of smart phones and tablets to interconnect to company email, calendaring and other services can blur the lines between company controls and consumer controls. Employees who are approved to have access to company information via their personal devices should understand and accept the limitations imposed by the company.
7. Govern Social Media. Active governance can help make sure employees speak within company guidelines and follow data privacy best practices.
8. Protect Remote Access. If your employees are allowed access to your private network from remote networks, this access should only be through a firewall that protects your private network. Another option is to utilize a Virtual Private Network (VPN) that uses encryption and multi-factor authentication to provide greater security.
9. Report Security Incidents. All employees and contractors should know the procedure for reporting incidents of malware and what steps to take to help respond.
What else can you do? Look into a Cyber Insurance Policy and if you already have a Cyber Insurance Policy, we should make sure you have the appropriate coverages. Contact us and we would be happy to help.
